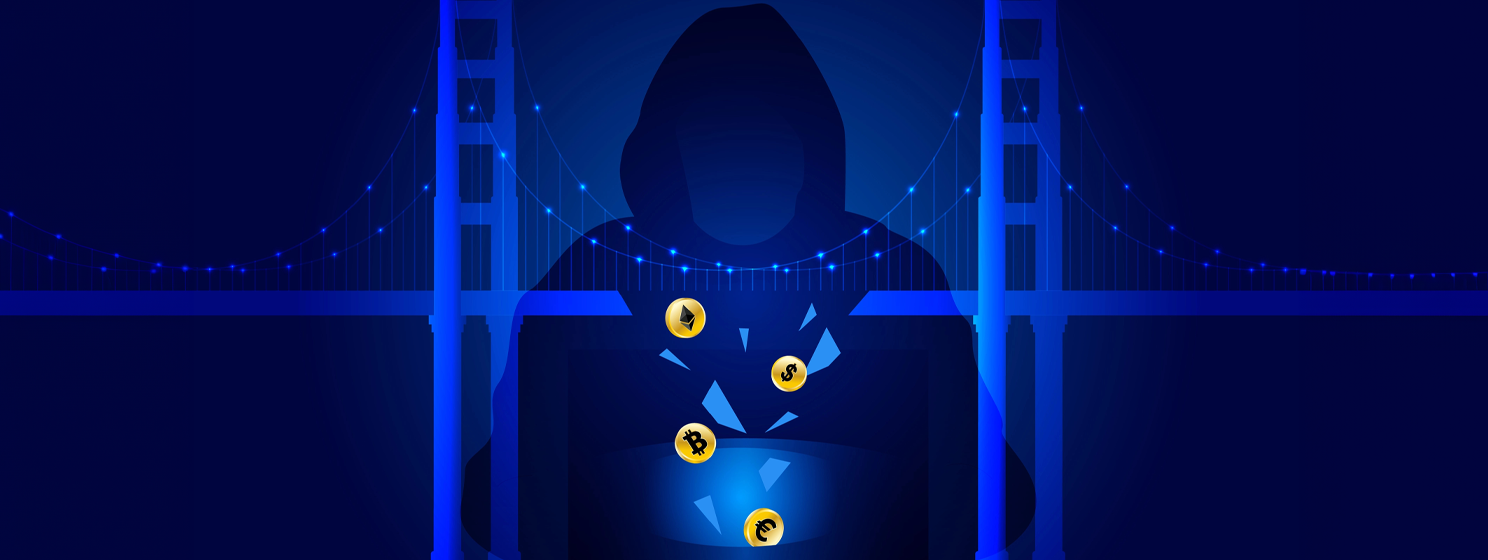
arbitrage attack
DeFi under scrutiny after flash loan trades expose system’s vulnerabilities
An anonymous market manipulator instigated a sophisticated arbitrage attack against the bZx decentralized finance lending protocol.
Viewing 1-1 out of 1 articles
Recent
Trending
Most Views

 05-23-2026
05-23-2026