Microsoft Security Intelligence
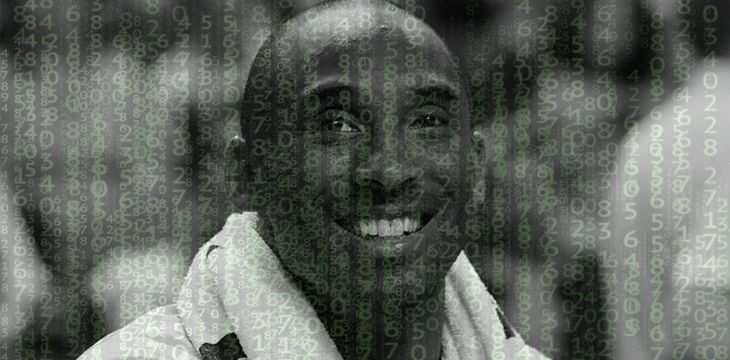
Scammers take advantage of Kobe Bryant’s death to steal crypto
Downloadable wallpaper featuring the athlete contains crypto-stealing malware.
Viewing 1-1 out of 1 articles
Recent
Trending
Most Views

 06-02-2026
06-02-2026