Article by Xiaohui Liu
-
3 October, 2023
Integrate Ordinals with smart contracts on Bitcoin: Part 4
In this article, sCrypt demonstrates how to control the distribution and issuance of BSV-20 tokens after minting such tokens.
-
2 October, 2023
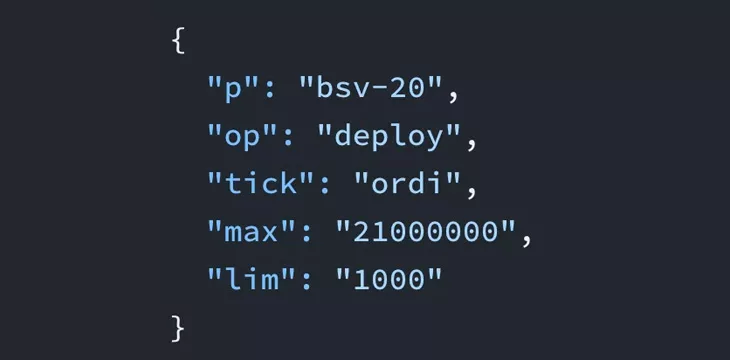
Integrate Ordinals with smart contracts on Bitcoin: Part 3
In this article, sCrypt shows how to integrate Bitcoin smart contracts with Ordinals with the fungible version, i.e., BSV-20 tokens.
-
29 September, 2023
Integrate Ordinals with smart contracts on Bitcoin: Part 2
To showcase ways to integrate ordinals with smart contracts, sCrypt developed a system that enables the on-chain auctioning of an...
-
28 September, 2023
Integrate Ordinals with smart contracts on Bitcoin: Part 1
sCrypt shows how to add smart contract capabilities to Ordinals, noting that Ordinals are compatible with smart contracts and perfectly...
-
27 September, 2023
Sealed auctions on Bitcoin
Due to the advent of blockchain technology, sealed auctions can now be implemented on-chain, offering a number of advantages over...
-
4 August, 2023
Cross-chain atomic swaps without Hash Time Locked Contracts
Cross-chain atomic swaps can now be done on blockchains lacking hash locks and time locks using SPV and Full Protocol...
Recommended for you
As sCrypt says, these proposals aim to enable Bitcoin's limited functionalities rather than tackling the broader need for expressivity and...
February 12, 2025
sCrypt has created a smart contract operating similarly to the hashrate escrow mechanism in Bitcoin’s Drivechain proposal.
February 10, 2025

 05-28-2026
05-28-2026