|
Getting your Trinity Audio player ready...
|
In early December, 280,000 of these devil bots went live during a 12-hour period.
If you’re running some mining rigs, make sure to check your configurations regularly. Satori, a botnet known to target Internet of things (IoT) devices such as routers and security cameras is now targeting miners—inconspicuously switching the owner’s wallet address to one that belongs to the hacker, effectively robbing the miner of his coin earnings. This is unprecedented, according to a report by Netlab 360, since previous malware target information to infiltrate wallets themselves and rob funds from there.
“What really stands out is something we had never seen before, this new variant actually hacks into various mining hosts on the internet (mostly windows devices) via their management port 3333 that runs Claymore Miner software, and replaces the wallet address on the hosts with its own wallet address,” they wrote in a post last week.
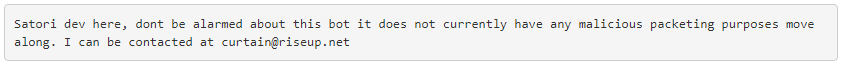
The new strain of worm-style malware, dubbed Satori.Coin.Robber, is breaking into miners’ systems configuration through a vulnerability in the Claymore Miner software for Windows, and has been targeting ether (ETH) earnings. Eerily, the author of the malicious code even sends the infected miners a message in an attempt to steer them from purging out the malware.
Netlab 360 says that the malware was actually deployed en masse in December, with over 280,000 bots going live from different IP’s within a 12-hour period, which means there could be far more by now. Even more disturbingly, a report from ZDNet says that the malware code for the nasty botnet’s predecessor—which targets Huawei devices—was circulated like some giveaway over the holidays. Whether Satori.Coin.Robber was circulated, and how widely is yet to be known. But Netlab 360 says there was a spike in scanning activity consistent with the Coin Robber early January.
We will post an update on how to resolve the issue for those who are infected.

 05-19-2026
05-19-2026 




