|
Getting your Trinity Audio player ready...
|
Merchants can accept payments with confidence when engaging in instant transactions, as Bitcoin SV is suited for real-world trade.
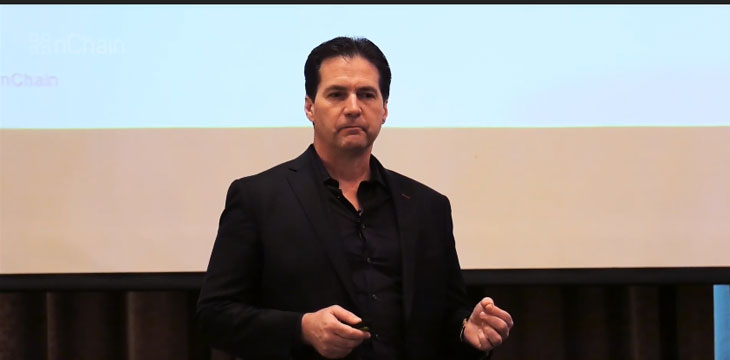
nChain chief scientist Dr. Craig Wright explained in a blog post that double spend attacks, where a payment only appears to be made but with money going elsewhere after delivery of a product, are avoided by measures already in place.
“Mining is there to ensure the creation of a competitive system to stop double spending… Miners are paid to not only verify transactions, but to find errors in the efforts of other miners, and to invalidate these,” he said.
Among items in a merchant’s invoice would be a minimum miners’ fee. “If the client hands the merchant a transaction using less than this, they will reject it,” Wright said. “It is the merchant and not the user who sets the terms used here, and the merchant can simply not allow the sale, if it is under the offer price.”
Wright enumerated several steps of a transaction which a double spend attacker would have to overcome, with most everyday products, such as a cup of coffee, not being worth the cost and effort involved.
With terms established between buyer and seller, either party could opt out if the other’s obligations are not fulfilled. “In the real world, a merchant or vendor gives you an invoice to pay. This does not change in the Bitcoin world. You send what is requested,” he said.
In the event that a merchant detects a double spend, through sending a request to the mempool, Wright said the payment is considered fraudulent, and that merchants have the right to detain the customer before having them taken to government authorities, “just as is the case with shop lifters right now.”
He said, “The reality is that in 2 seconds (or less) the merchant has checked the transaction, and the reality is that you do not get to send a double spend,” adding, “I will cover any loss that occurs on a REAL double-spend fraud. Oh… I do not expect to even have to spend a cent. I will also help ensure that the person who does it ends spending a long time in a small cell.”
Wright also pointed out that keys should not be reused, where an address is used for more than one transaction. “If users simply did not use the same address more than once (ever), the idea of tracking ‘spam’ payments would not exist at all,” he said.

 05-28-2026
05-28-2026